Privacy control plane for data in motion
Make outbound data useless if stolen.
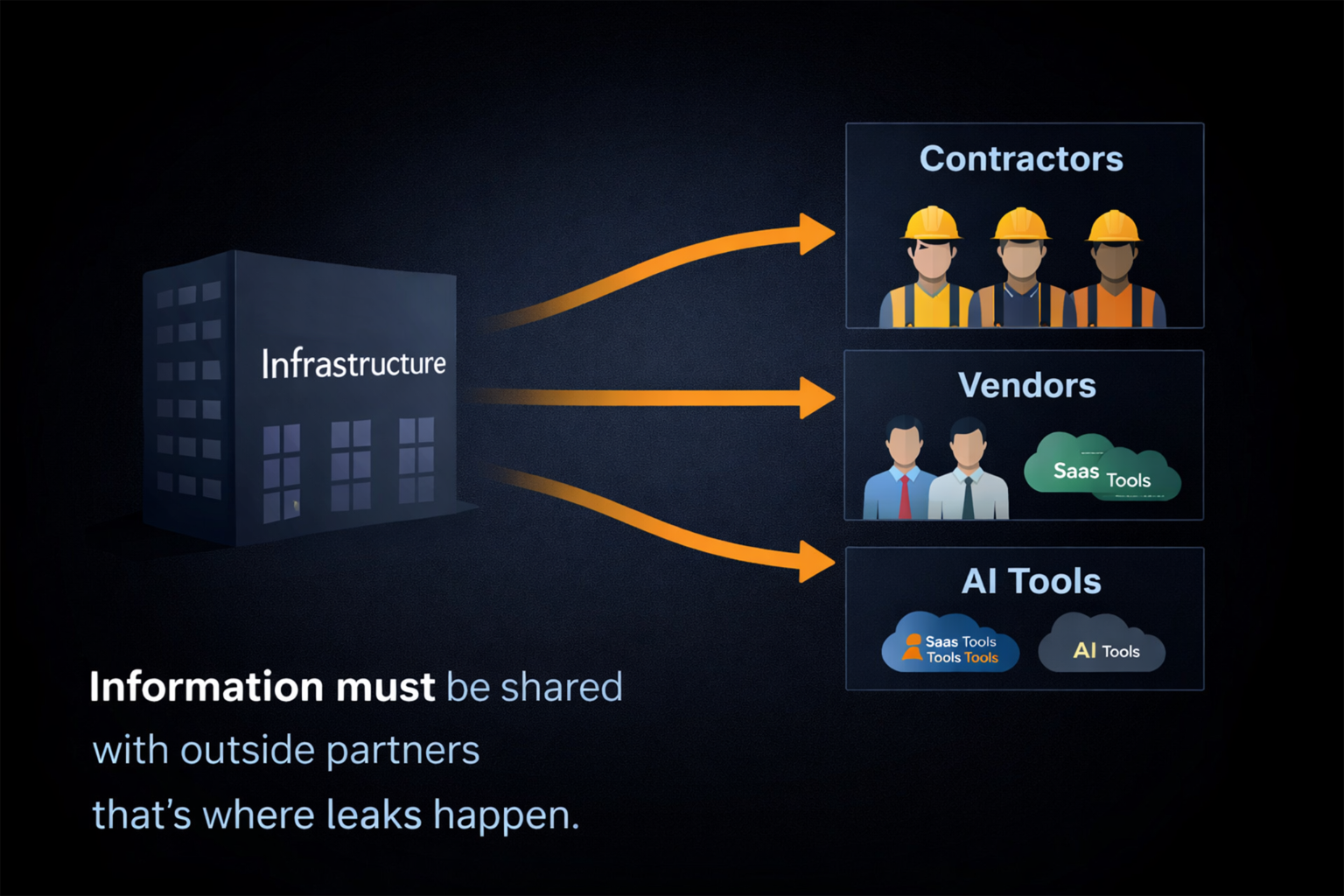
Contractors, SaaS vendors, and AI tools need access to operational data - that's where leaks happen.
iRNDOM swaps sensitive identifiers for safe labels before data leaves your boundary. Restore is internal-zone only,
cryptographically verified and fully audited.
Safe Labels™
Protect outbound
Verified Restore™
Internal-zone only
Zone Gates™
No vendor restore
Signed Audit™
Proof per request
Gateway: Online
Sidecar: Online
Audit: Enabled
Data must be shared with outside partners & that's where leaks happen
Critical infrastructure sends data to contractors, vendors, and AI tools every day. The moment it leaves your environment, you lose control but keep the liability.
Where breaches explode
Vendor systems & logs
Compromised SaaS accounts
Export files & support tools
AI workflows that copy data
What you want instead
Outbound data is safe by default
No vendor-side restore paths
Least-privilege internal restore
Audit proof per request
How iRNDOM works
Drop-in gateway + sidecar vault. No vendor change required.
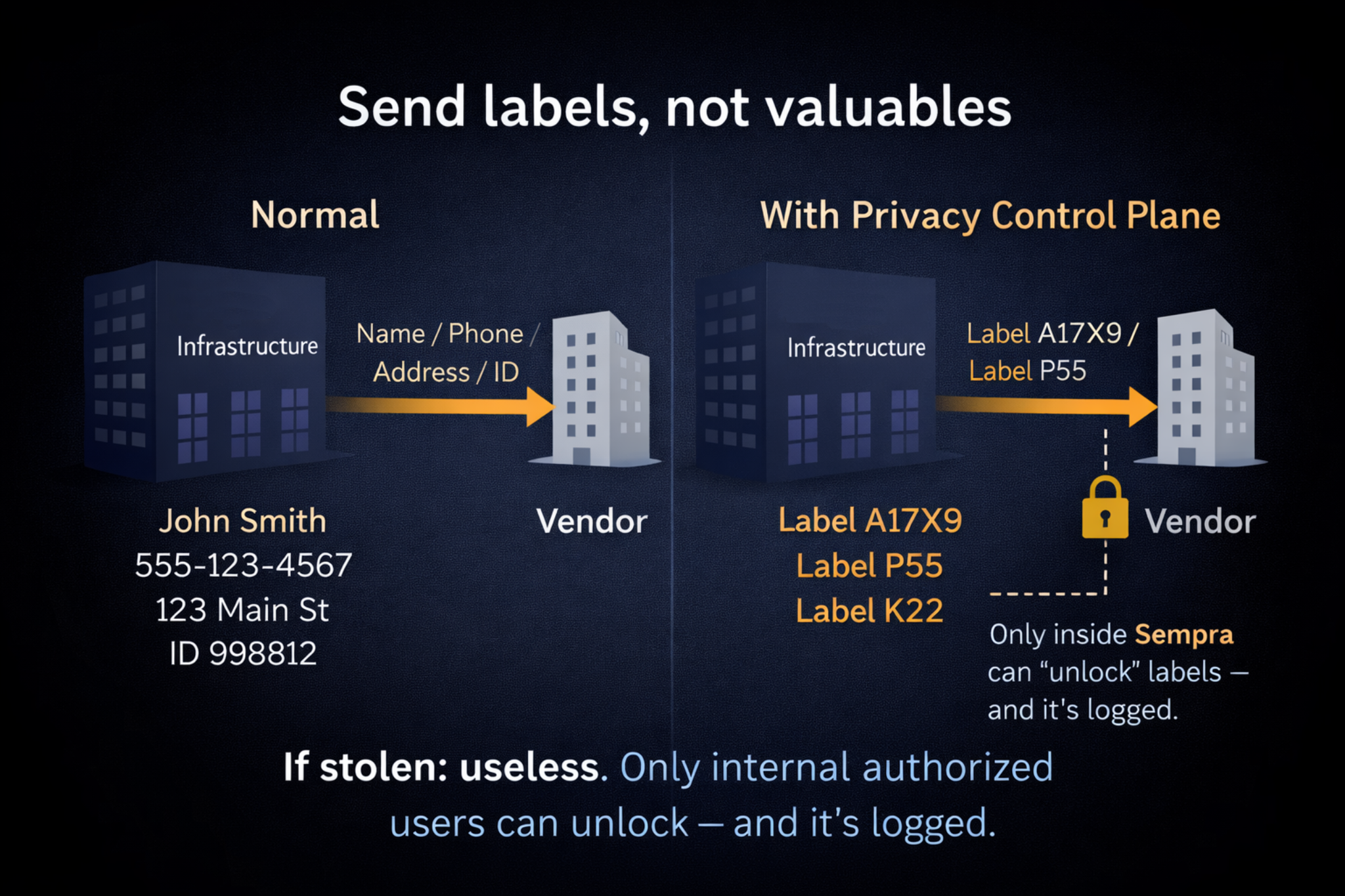
1. Apply Safe Labels™ on the way out
Sensitive fields are replaced with labels before the request leaves your boundary.
2. Store mappings internally
Protected mappings stay under your control inside the approved deployment boundary.
3. Restore only in the internal zone
Restores require signatures, zone policy, and produce an audit proof trail.
Key idea
Encryption protects transport and storage. iRNDOM protects usage by ensuring outside systems only ever see non-sensitive Safe Labels™.
What vendors see vs what internal systems see
Same payload shape. Different meaning depending on zone + authorization.
Designed for operational workflows
Join, track, and match on Safe Labels™
Use Safe Labels™ for ticketing, analytics, and AI
If a narrow use case needs originals, restore is internal-only
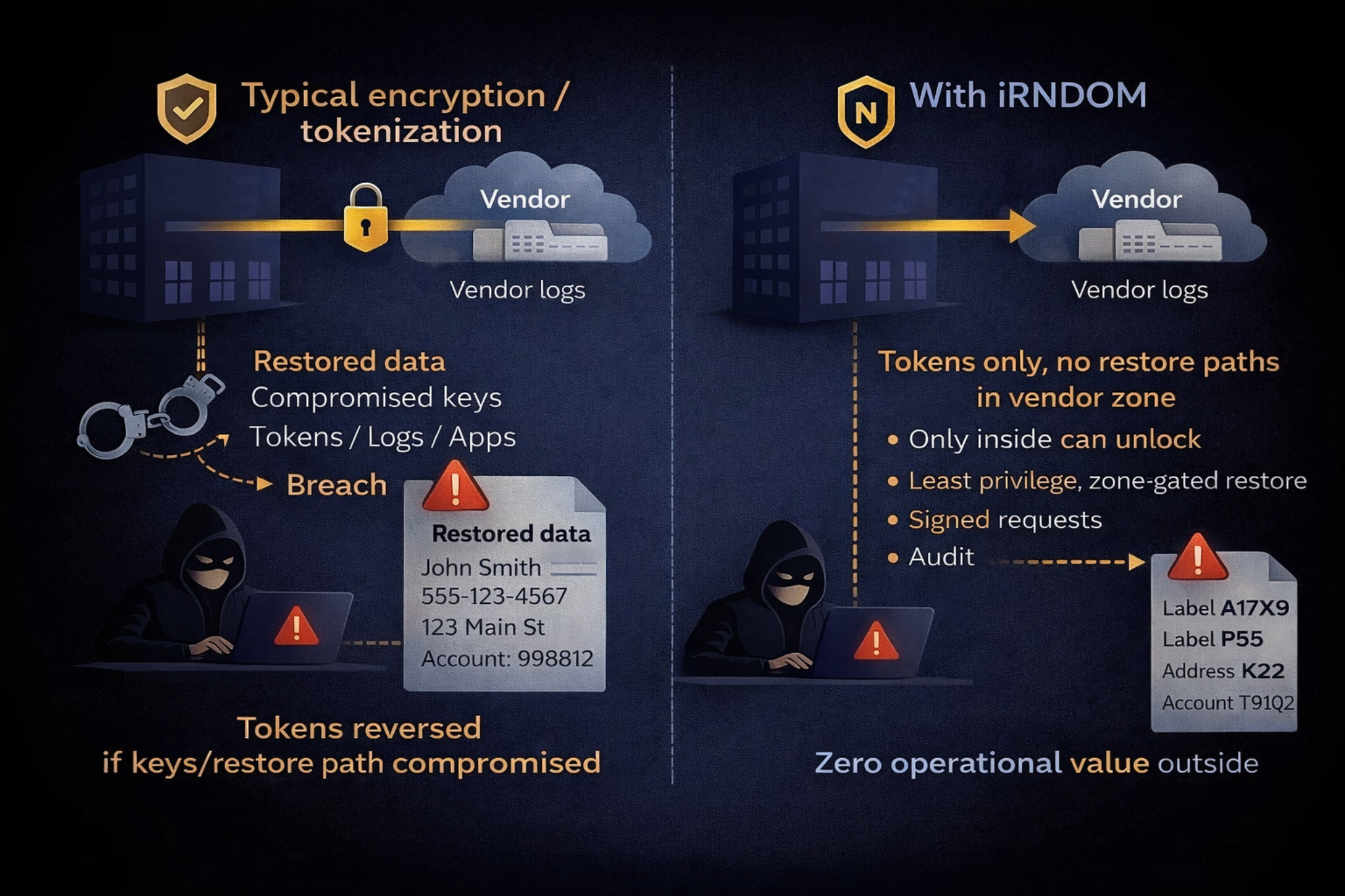
Incident response gets simpler
Stolen vendor logs have zero operational value
Audit evidence exports (policy + proofs)
Least privilege + zone enforcement by default
Controls that matter to security teams
Practical controls for third-party risk, auditability, and breach blast-radius reduction.
Zone-based enforcement
Vendor zone is label-only. Restore is internal-zone only.
Signed requests
HMAC signatures validate caller identity and prevent tampering.
Replay protection
Nonce + timestamp checks block replays (demonstrated in Live Demo).
Audit proofs
Every decision logs evidence for compliance + incident response.
Rate limits
Protect sensitive endpoints from abuse and credential stuffing.
Exportable artifacts
Generate policy + audit bundles to attach to procurement/security reviews.
FAQ
Short answers for non-technical stakeholders. Technical depth is available in the demo + audit proofs.
Does this break vendor workflows?
Usually no. Vendors can operate on Safe Labels™ for matching, tracking, and joining. If a narrow workflow needs originals, restore can be permitted only for an internal zone with audit.
How is this different from encryption?
Encryption protects data in transit/at rest. Breaches often happen where data is used (vendor systems, logs, compromised accounts). iRNDOM reduces impact by ensuring outside copies don't contain real identifiers.
Where do token mappings live?
In the iRNDOM sidecar vault, which is deployed in your controlled environment. Vendors never get direct access to the vault.
Who can restore originals?
Only authorized internal callers. Restore requires zone policy + signatures and is logged with proofs.
How fast can we pilot?
A small pilot can start by routing one outbound integration through iRNDOM, identifying a few sensitive fields, and validating the protected output in the Live Demo.
Want to see the proofs?
The Live Demo shows Safe Labels™ replacement, internal restore, and blocked attacker scenarios (replay + signature tamper), plus audit evidence.